Gone Phishing – Email Scams at Marshall University
A text from an unknown number. An email from what looks to be an official organization. A link sent by a trusted colleague. Any of these could be an open invitation for cybercriminals to collect your personal data and begin taking whatever they like through a phishing scam.
While cybercrime is a risk everyone faces in an increasingly technologically dependent world, college students must deal with specific challenges to keep their personal and professional information out of the wrong hands.
Phishing scams are one of the most common forms of cybercrime, and they can act as an easy entry point for scammers to begin digging their way into a student or faculty member’s personal accounts and any organizations that the victim is a part of.
Phishing scams are a form of cybercrime in which individuals utilize email or pop-up messages to imitate a person or organization their victim likely knows and interacts with, such as a bank, to collect their information.
While phishing emails can vary significantly in their content and strategy, scammers often use a few common tactics to try and increase their chances of success. One of these is a false sense of urgency. According to Marshall IT, many of these scams will threaten “a dire consequence” if the user doesn’t respond.
These consequences can range from having their bank account shut down to something more specific like losing their financial aid. Still, the end goal is the same: to make the user panic and click on a link they may not usually trust.
“It’s just human nature. People get in a hurry, and, typically, that’s the negative effect from it,” said James Mynes, Marshall’s manager of information security operations.
Mynes explained that people being in a hurry is one of the biggest factors that can lead to them clicking a link that they shouldn’t.
Once a user clicks one of these false links, the scammers will then work to collect their personal information, often from an official-looking website meant to imitate whatever organization they’re posing as. And while these scams pose a major risk to the user’s personal information, they can also threaten larger organizations.
“Today, it is way easier to hack a person than it is a network, and so email phishing is one of the biggest concerns,” said Justin Jarrell, a cybersecurity consultant and the CEO and co-founder of Forge, an Appalachian-based cybersecurity consulting company.
Jarrell has spent over a decade working in cybersecurity with groups such as the Department of Defense and other large organizations, and even at this scale, he still sees phishing scams as a major cybersecurity concern.
Today, it is way easier to hack a person than it is a network, and so email phishing is one of the biggest concerns. — Justin Jarrell
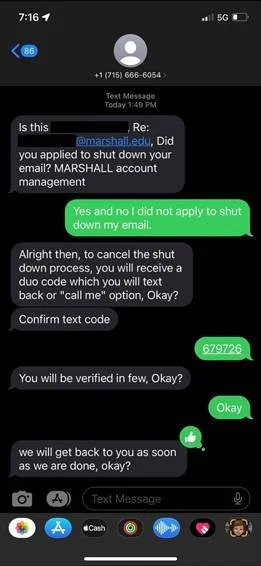
Below are a series of phishing scams sent to Marshall faculty and students provided by Marshall’s IT department. Marshall IT regularly uploads phishing scam stories to their Phish of the Day News Archive at https://www.marshall.edu/it/category/infosecalerts/phish-bowl/
Phishing scams aimed at Marshall students and faculty are unique compared to messages sent to personal accounts or through other platforms for various reasons.
The first is that Marshall has a dedicated team of IT professionals working to keep university members safe from cybercrime.
“If you have a Gmail account, there’s not really a team of people that are sitting there monitoring trying to make sure you’re not getting scammed, whereas we very much do that here,” Mynes said. In addition to IT monitoring, the university utilizes Microsoft’s security systems to help block scam emails that other organizations or universities may have reported.
Another difference is the availability of information. Due to the interconnected nature of Marshall’s emails, one compromised address could have wide-ranging consequences for others in the network.
“Did somebody have a contact list, and their account was compromised, and the bad actor’s going for what’s of value?” said Jon Cutler, Marshall’s chief information security officer. “If their inbox has the spreadsheet with everybody that’s on the rugby team or the chess club or everybody that took freshman English, then that would be an interesting thing for us to know to say, ‘Hey, here’s a common thread,’ everyone in this one cohort is being targeted.”
Lastly, Marshall’s emails are unique due to the information scammers can use to target students.
“In many cases, the bad actors do their homework. They know on a college campus what are important topics. They know what systems we use,” Cutler said. While some scammers settle for broad, non-specific emails sent to large, undefined groups of email addresses, others have targeted campaigns aimed at specific groups. This begs the question: what do scammers want from phishing scams?
The short answer? Money. The primary motivation behind most phishing scams is financial. According to Mynes and Cutler, cybercriminals primarily work toward a financial goal, directly or indirectly.
A direct approach would be to try to steal something like bank account information. In contrast, a more subtle option might be to take your data to sell elsewhere on the internet.
On the other hand, there are sometimes more specific motivations that IT professionals and individuals need to keep in mind. Individuals holding specific grudges against an organization might use cybercrime to lash out against them.
“The groups that scare us are the folks that are: ‘I’ve got an ax to grind with Marshall,’ and if you get targeted, it’s very difficult to be hack-proof,” Cutler said.
And while these specific targets are certainly a concern, scammers often take what they can get.
“The crime, in and of itself, is a crime of opportunity, meaning these cybersecurity criminals, what they’re doing is no different than walking down the street and pulling a car door handle to see if the car is unlocked,” Jarrell said. “It is so easy to hack a person and, as a result, gain access to sensitive material to exploit that it is, metaphorically, as easy as pulling a car door handle to see if the car is unlocked.”
While Mynes, Jarrell, and Cutler all provided different metaphors to explain the motivations and consequences of cybercrime, they all circled back to one central idea stated by Cutler: “Even though this takes place in the digital realm, it is a crime.”
Despite the seeming complexity of cybercrime, many of the motivations and techniques utilized by cybercriminals are no different from the crimes that occur in the real world.
From changing passwords to having private information stolen, students at Marshall face a variety of phishing scams from multiple platforms.
Many of these come through their Marshall email and use appealing language, offering things like “exciting job opportunities.” Others take a more official approach, directly imitating Marshall or Marshall offices to convince students to hand over their official login information.
For some students, the scams can be even more sinister in nature. One Marshall student retold the story of her email being hacked shortly after her father’s passing. An email was sent to her father’s personal account posing as necessary information. After taking her and her sister’s personal and student emails, the perpetrator hacked into their emails to trick other people into clicking unsafe links.
Marshall IT eventually resolved the issue using a new password, but this shows that personal and student email hacks are not mutually exclusive and can overlap significantly.
Students must also be aware of their information on other platforms, as this information can be compromised through phishing or other means.
“Definitely on social media. I know that’s been a big problem with a lot of my friends getting their accounts hacked,” Indigo Graves, a Marshall freshman, said. With all these different platforms offering various levels of security and protection, students must be aware of where their data is stored and how to best protect it.
Every cybersecurity and IT expert has a unique method of educating the public on protecting themselves and their personal information online. According to one of Marshall IT’s main awareness campaigns, it starts with three words: Stop. Think. Connect.
Marshall IT recommends that students and faculty first stop and think about what is being asked of them, fighting back against the false sense of urgency created by many phishing scams. According to Cutler, many of these emails don’t make sense when viewed with a critical eye.
For example, suppose an email threatens that your financial aid will be taken away in 24 hours. In that case, this is likely a scam, as the Financial Aid Office would most likely reach out multiple times over various forms of communication before taking such a drastic step.
Suppose the victim still feels unsure of the email’s validity. In that case, the next step is to connect by either reaching out to the organization or individual directly or even contacting IT to see their thoughts.
“You’re not going to get in trouble if you call IT and say, ‘I think I might have done something wrong.’ I can say, unequivocally, we want to help that person to get through that because it’s their information, it’s the university’s information, and we all have a stake in making that a good situation.” Cutler said.
From a more general perspective, Jarrell provided a list of recommendations he would give to students interested in protecting their information online.
These include privating all social media accounts, only messaging people you know directly, avoiding advertising emails (even from well-known brands), not clicking links in emails and making passwords at least 16 characters long.
“The greatest password bots can hack a 14-character password in about 11 minutes or less. Once you bump up to 16 characters, it takes those same bots that are working on servers about 23 hours,” Jarrell said.
Because of this, cybercriminals will often give up if their password hack takes more than ten minutes, providing an extra layer of protection for personal information.
Lastly, one of the most potent tools in cybersecurity is two-factor authentication, which requires logins to be performed using more than one device or account, usually involving a confirmation code sent to the user’s phone during the login.
Marshall IT uses this tool extensively to protect emails, and Jarrell argues that it is one of the best tools at an organization’s disposal. However, cybercriminals may also try to find ways around this security message.
A technique known as “smishing” involves fraudulent messages sent over text, and this is one technique cybercriminals may use to try to get into networks that utilize two-factor authentication.
The same techniques for protecting oneself from phishing still apply here, though, and with a critical eye, students and faculty can work to defend themselves on all platforms.
The future of phishing and cybercrime are directly tied to the future of technology. Though increasing awareness campaigns and exposure to phishing scams may give an impression that phishing is becoming more common, Jarrell argues that this perspective is missing the big picture.
“The reason it seems worse is because we’re using IT more in our lives. The convenience that it has brought has now elevated from convenience to necessity. So, as a result, when things go wrong, it feels a lot bigger. So, yes, we’re getting hacked more, but that’s only because it’s hard to differentiate. Are we in the cyberspace more, or is it actually getting worse?” Jarrell said.
As technology becomes an increasingly important part of people’s lives, the potential gain for cybercriminals becomes greater. According to Mynes and Cutler, AI tools can also make it easier for scammers to develop their hooks, collecting and inserting data to quickly create emails and prompts that are unique to individuals.
The pervasive nature of these scams requires anyone interested in protecting their information online to remain vigilant. Scammers will do anything they can to collect this information. Without careful consideration, it’s all too easy to fall for their traps hook, line and sinker.
Your donation will help continue the work of independent student journalism at Marshall University. If you benefit from The Parthenon's free content, please consider making a donation.
Thank you for your donation!